- Illumio Core 23.5 Install, Configure, Upgrade
- Kubernetes and Openshift
- Configure Security Policies for Containerized Environments
- Liveness Probes
Liveness Probes
Liveness Probes
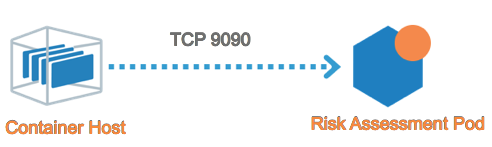
Containerized applications may require periodic health checks known as liveness probes and readiness probes. Each application includes a health check YAML file that contains configurations for liveness and readiness probes. The health checks between the container node and the local container workload may rely on TCP ports. Illumio has included a source object called Container Host for this use case. The Container Host object represents the container node or nodes that host the Pod(s). The example below uses the Container Host object as a source for Liveness and Readiness Probes.
Note
The Container Host must always fall under an Extra-Scope rule.
The rules you need to write are:
Kubernetes and OpenShift
The rules you need to write are:
Example Ruleset
Scope
Application | Environment | Location |
|---|---|---|
Risk Assessment | Development | Cloud |
Extra-Scope Rule
Source | Destination | Destination Service | Notes |
|---|---|---|---|
Container Host (built-in Illumio object) | All Workloads | TCP 9090 | In this example, the Risk Assessment health check configuration indicates that the liveness probe occurs on TCP 9090. Liveness probe ports/protocols may vary across applications. Container Host is an object built into the PCE by default and represents any node that hosts the respective Pod(s). |